Security and Privacy in Mobile Devices
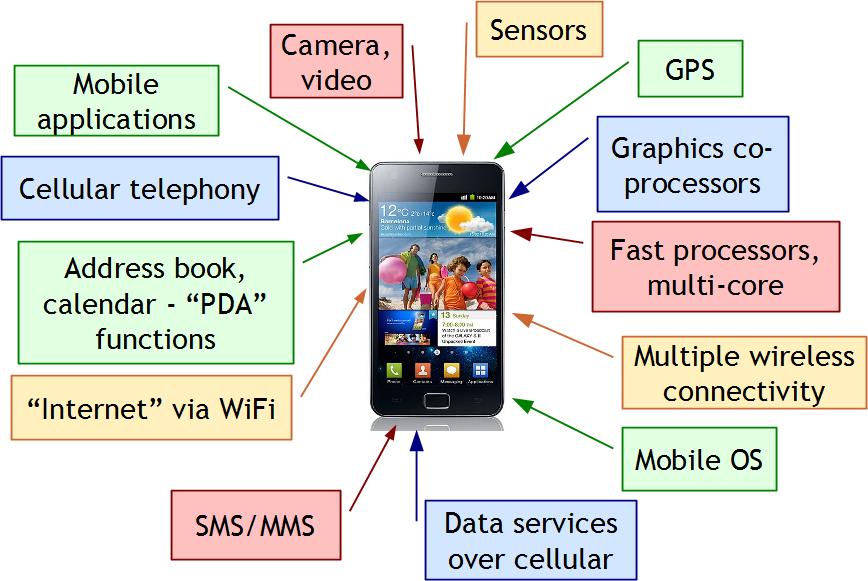
The quick rise in mobile device use has lead to the emergence of a wide variety of security and privacy issues that are close at hand to a large portion of the world's population. Modern mobile devices, however, are more than just telephones, more than computers, more than sensor-rich devices, and more than any other electronic device that has been on the market to date. They rely on a telecommunications infrastructure that was not designed with the diversity of rich applications and services that have emerged, so there is a fundamental mismatch between security models used in their design and the reality of the mobile space. Instead of treating mobile devices as "a telephone that runs apps" or "a computer that makes phone calls", we treat them as a system-of-systems with deep interactions and dependencies among component systems. Along these lines, we have been investigating various issues of security and privacy in telecommunications, personal area networking, near-field communications (NFC), mobile operating systems, mobile applications and permission models, and so on.
Security & Privacy in Mobile Apps and Services
Smartphones have forever changed the mobile telecommunication and computing landscape. Mobile operating systems now support a diverse set of applications and services provided by major software providers as well as third-party developers around the globe. However, the unique system-of-systems nature of smartphones and tablets, comprising communication, networking, sensing, actuation, storage, navigation, and various other features, break the typical computer security, communication security, and network security definitions and force a drastic re-imagining of mobile security and privacy. Our work focuses on these aspects of mobile security that do not align with the existing definitions and models.
Related Publications
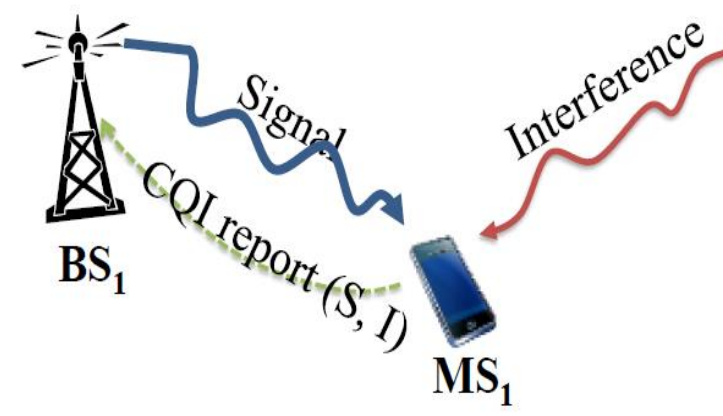
Telecommunication System Security
Telecommunication systems have evolved significantly and rapidly in recent years. Since much of the evolution has been pushed by customer demand for higher quality and faster data rates, service providers have often overlooked threats and vulnerabilities in their system designs in favor of faster response to customer needs. In an effort to push for more reliable and resilient telecommunications, we have studied a number of such threats and vulnerabilities that can be addressed using practical techniques that do not incur significant overhead or modification to production systems. At a more fundamental level, we are also investigating deeper redesign of the telecommunication infrastructure to study alternatives that could drastically improve service quality to users, costs to service providers, and capabilities for all parties.