HiveGuard: A Distributed System for Monitoring the Security of Zigbee Networks
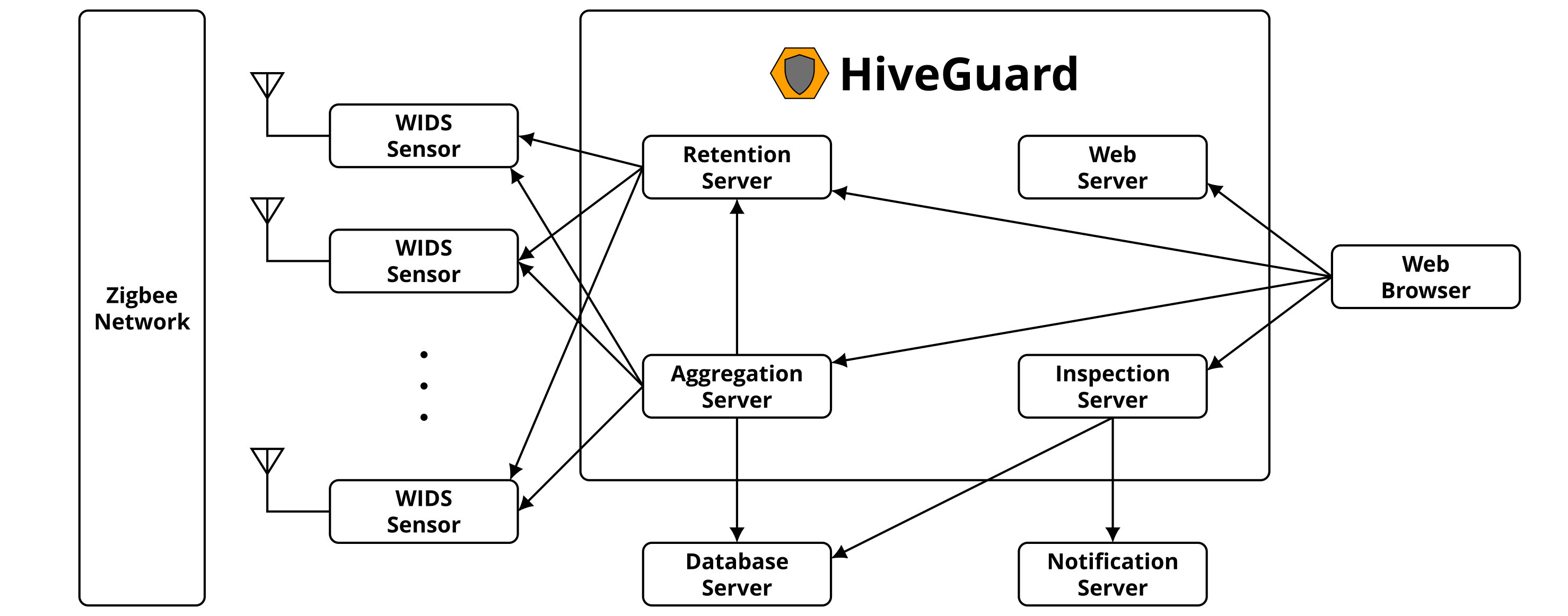
Although the Zigbee protocol is currently utilized by numerous smart home and smart building devices, Zigbee networks remain largely unmonitored, which means that malicious users can launch several types of attacks against them and go undetected by their network administrators. HiveGuard is a network security monitoring system for Zigbee networks that we developed in order to provide archiving, aggregation, inspection, visualization, and alert services by interacting with a set of wireless intrusion detection system (WIDS) sensors, a database server, and a notification server. In order to test the monitoring capabilities of our prototype implementation of HiveGuard, we also developed an energy depletion attack against battery-powered Zigbee devices. Our experiments show that it is possible for an outside attacker to completely deplete the energy of four commercial Zigbee devices, each powered by a brand new 3-volt CR2450 lithium battery, in less than 16 hours. During our experiments, HiveGuard was able to send us appropriate notifications for each attack that we launched against our Zigbee network. We responsibly disclosed our energy depletion attack and our related findings to the Connectivity Standards Alliance (formerly known as the Zigbee Alliance) in May 2021. The source code of our prototype implementation of HiveGuard has been organized into three publicly accessible repositories, while our dataset of captured Zigbee packets during our energy depletion attack experiments is available on CRAWDAD. We also conducted follow-up experiments in Spring 2022 with two commercial Zigbee devices that were powered by a brand new 3-volt CR2032 lithium battery and a brand new 3-volt CR2 lithium battery, which show that an outside attacker could deplete their energy in less than 7 hours and in less than 92 hours respectively.
Software
Dataset
Presentations
Energy Depletion Attack
In the following figures we provide an overview of our energy depletion attack, which we implemented by modifying the firmware of an ATUSB IEEE 802.15.4 USB adapter, and a screenshot of HiveGuard's header fields page, shortly after our energy depletion attack was launched against one of our battery-powered Zigbee devices.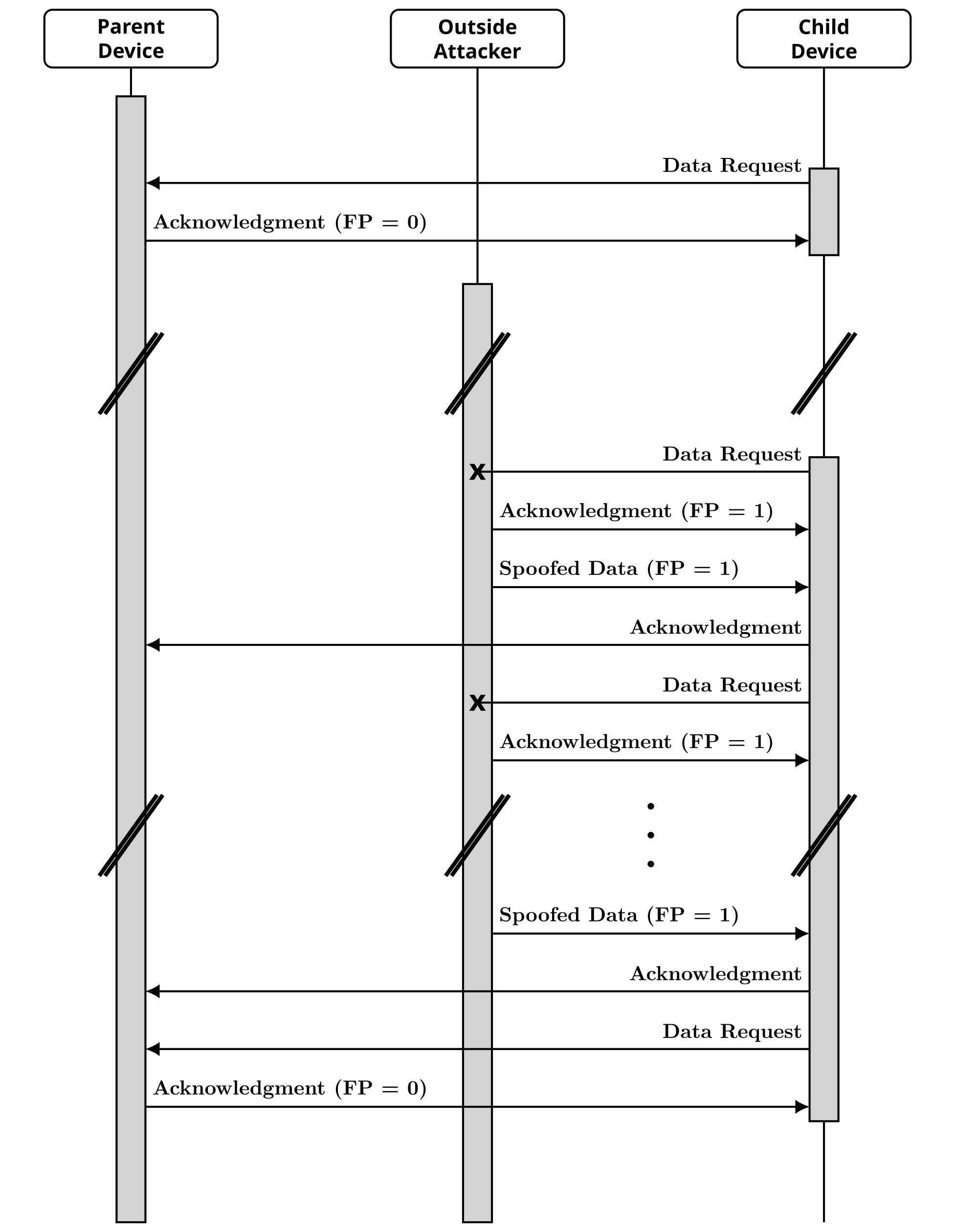
Our energy depletion attack improves upon the attack that Cao et al. presented. More specifically, our attack was specifically designed to exploit the way that Zigbee devices are currently handling Data Requests by selectively jamming them and injecting spoofed packets. We also introduced further improvements to the attacker's main strategy that prevent the targeted Zigbee device from disconnecting from its Zigbee network and make the aggressiveness of our attack configurable. Essentially, an outside attacker can prevent a child device (i.e., a battery-powered Zigbee End Device) from returning to its energy-saving sleep mode by selectively jamming its Data Requests and spoofing packets with supposedly encrypted and authenticated data, while repeatedly claiming that there are additional packets destined for that child device. Furthermore, the outside attacker occasionally allows the child device to communicate with its parent device (i.e., a Zigbee Router or the Zigbee Coordinator) to prevent the child device from disconnecting from its Zigbee network. You can find more information about the testbed that we used for our proof-of-concept implementation of our energy depletion attack in our ACM WiSec 2020 paper and on the Zigator project page.
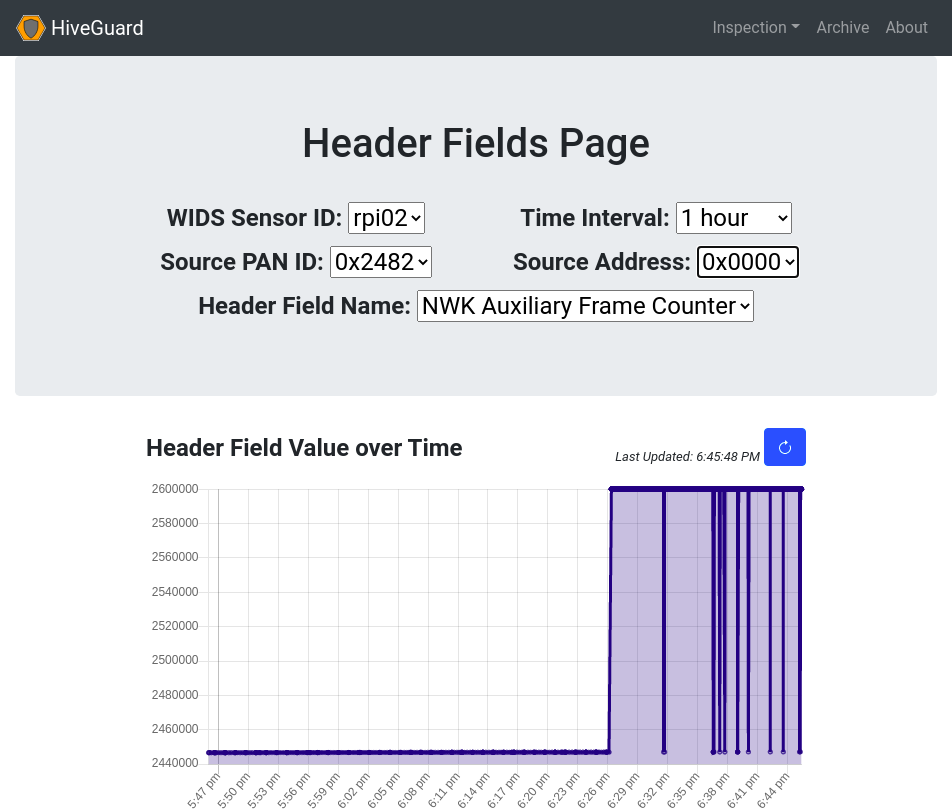
In order for the spoofed packets with supposedly encrypted and authenticated data that the outside attacker injects to be processed by the targeted child device, they must use a higher value for their NWK auxiliary frame counter header fields than the one that the corresponding parent device last used. However, the next time that the corresponding parent device will transmit a legitimate packet with NWK-layer security enabled, it will appear as if the value of the NWK auxiliary frame counter header field unexpectedly decreased over time. As we describe in our corresponding IEEE CNS 2021 paper, HiveGuard's inspection server used this pattern to detect the energy depletion attack and alert us that a nearby device may be impersonating our Zigbee Coordinator, while HiveGuard's frontend application enabled us to further examine the operation of our Zigbee network.